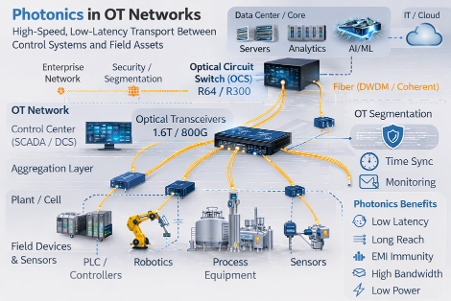
Photonics is the use of light for communication, switching, sensing, and in some cases computation. Photonic computing is no longer an unobtainable, futuristic technology. In operational technology (OT) security, we can deploy photonics now: namely fiber transport, optical switching concepts, optical-layer telemetry, and fiber-based sensing.
Zero Trust Architecture (ZTA) and OT security don’t always line up cleanly because OT environments operate under constraints that most enterprise networks simply don’t have. OT has deterministic operations, safety implications, and availability requirements that add increased complexity. OT also has long asset lifecycles and legacy protocols that were never designed for authentication, encryption, or contemporary approaches towards logging, not to mention the physical limitations OT brings to the equation.
At the same time, national security and defense guidance is pushing OT and control systems toward modern security outcomes aligned to ZTA. According to the Department of Defense (DoD) Zero Trust Strategy “The journey to Zero Trust requires all DoD Components to adopt and integrate Zero Trust capabilities, technologies, solutions, and processes.”
This post breaks down where photonics supports OT Zero Trust outcomes and what current industry trends indicate about the optical infrastructure OT which environments are built on.
OT Zero Trust conversations often revolve around a similar theme. Security teams describe the end state: almost always tighter segmentation, fewer implicit trust paths, stronger monitoring, reduced lateral movement, controlled access, and faster detection and response.
Then an engineer asks the operational question: “How do we do that without breaking XYZ?”
In OT, availability is the mission. If a control adds jitter, creates chokepoints, or complicates recovery, it will be bypassed, even if the policy says otherwise. OT systems do not tolerate fragile security. They simply can’t afford to.
Photonics keeps showing up in these discussions because it allows for “security by physics” rather than “security by complex configuration”, which is an attractive selling point for overburdened OT staff. Fiber transport improves link stability and reduces electromagnetic susceptibility but it also eliminates the need for expensive shielded cabling, permitting much longer reach in massive industrial footprints. That stability makes segmentation more durable, which reduces the temptation for temporary bypasses. Optical-layer telemetry provides link integrity signals that help during incidents. Optical switching patterns support a zero-trust idea which OT can feasibly adopt: connectivity that is explicit, time-bound, and auditable, not permanently ambient.
Additionally, photonics can even help organizations improve metrics and enhance security strategy even from a governance perspective. For example, photonics reduces Mean Time to Repair (MTTR) by using “link truth” signals to instantly distinguish between a physical fiber break and a cyber-attack.
(Created by author using gen AI)
1.6T silicon photonics transceivers and related building blocks: Coherent has publicly showcased silicon photonics based 1.6T-DR8 modules in Octal Small Form-factor Pluggable (OSFP), highlighting a differential electro-absorption modulated laser (D-EML) aimed at reducing power and crosstalk for higher-speed links.
(Courtesy Coherent) https://www.coherent.com/news/press-releases/400g-differential-eml
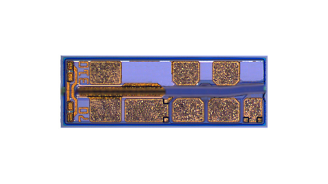
Coherent’s product direction signals a broader architectural trend away from “always-on, broadly reachable networks” toward intentional, on-demand pathways that can better support least-privilege connectivity, time-bound access, and smaller blast radius, while the maturation of high-integration pluggables helps make durable segmentation backbones more practical and supportable over time.
Lumentum is more concentrated in optical communications and photonic components, best known for indium phosphide–based lasers and modulators that power high-speed optical links, as well as optical switching and related infrastructure used in modern network fabrics. They are a strong lens on the building blocks that make dense, reliable optical connectivity possible at scale.
Some of the latest designs highlighting zero trust capabilities include:
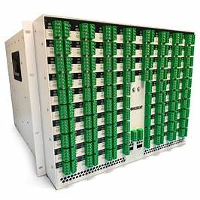
R64 Optical Circuit Switch: Lumentum announced and productized an R64 platform, positioned as a lower port-count OCS built on field-proven micro-electromechanical systems (MEMS) technology
(Courtesy Lumentum) https://www.lumentum.com/en/products/64×64-optical-circuit-switch-ocs

Optical circuit switch portfolio messaging: Lumentum’s OCS materials emphasize transparent any-to-any connectivity with low latency, low insertion loss, and low power consumption, built on MEMS.
(Courtesy Lumentum) https://www.lumentum.com/en/products/300×300-optical-circuit-switch-ocs

Lumentum’s newest photonic technology also points to a broader trend toward intentional, on-demand, while its continued push in 200G-per-lane electro-absorption modulated laser (EML) components reflects the maturity curve that makes optical infrastructure more reliable and supportable for durable segmentation backbones over time.
OT is now inside the zero trust execution perimeter and the Department of War (DoW) has described OT-specific activities and outcomes that make the expectation concrete.
Photonics assists OT security teams achieve more favorable outcomes with fewer operational tradeoffs:
For mission partners, the value is straightforward. Photonics is not the story. OT outcomes are the story. Photonics is one way to make those outcomes operationally survivable.
OT will not suddenly become photonics-native. However, it most certainly will become photonics-assisted.
Near-term adoption trends will likely look like:
The best OT programs will not use photonics because it sounds futuristic. They will use it because it makes the right outcomes easier to sustain.
OT zero trust is not a checkbox exercise. It reduces implicit trust without breaking operations.
Photonics does not replace identity, access control, boundary enforcement, or incident response. It makes segmentation more durable, monitoring more confident, and controlled connectivity more achievable. It also forces a healthy truth: in OT, you cannot separate cyber from physical, and you cannot secure what you cannot observe.
Security that breaks the mission is not security. Photonics helps us get closer to the version of OT zero trust that actually works.